FluBot Android malware, discovered in December 2020 in Spain, has, like the Spanish Flu, migrated to Australia. It is essentially banking malware now with customisation for many Australian bank apps. It looks like an iPhone variant may exist as well.
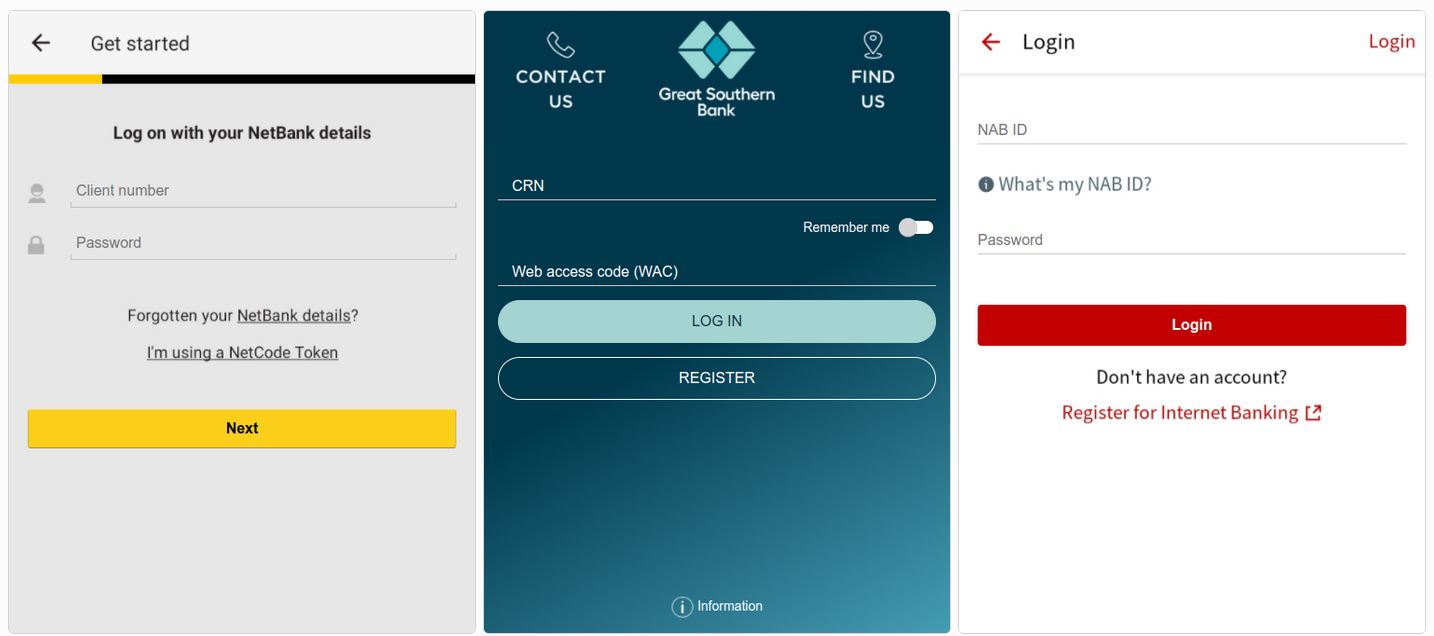
According to ESET, those bank apps include Bank Australia, Bank of Melbourne, BankSA, CommBank, Great Southern Bank Australia, HSBC Australia, National Australia Bank, St.George Bank, Suncorp, and UBank. And many more are in the pipeline purporting to be from courier delivery companies, Telcos, or other services.
How do you catch FluBot?
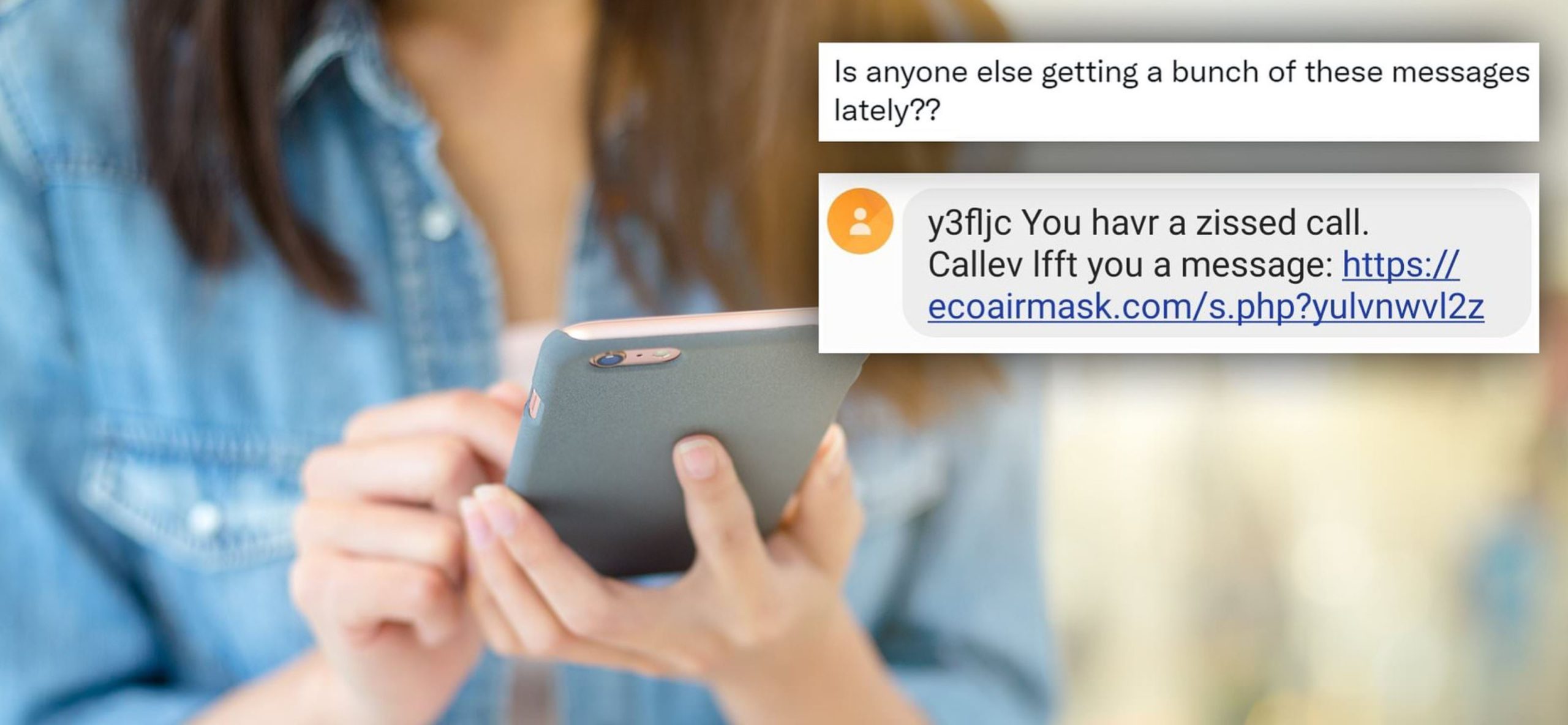
It gets onto the Android phone via clicking on an SMS link to the bank app or another service provider like voice mail. To stop it, don’t click any link and delete the SMS.
The malware, once installed, does many things
- It goes back to a command-and-control server for instructions – that could be to download the latest customised versions for more service providers that have an app in Google Play
- Take you to an authentic-looking log-in site where you enter your name and password (to help with ID theft)
- Send similar poisoned link SMSs to your contact list (it Is self-replicating)
- Other malware can steal passwords, contacts, email and much more.
What to do to if you think you have it
Don’t click any link and delete the SMS.
There may be obvious signs like new icons (bank or service providers) that cannot be uninstalled. Or you may get calls from friends asking why you sent them an SMS.
Install ‘paid’ Android malware protection from companies like ESET, Kaspersky, Norton LifeLock or McAfee. All can detect and remove it.
If you can’t afford paid malware protection, backup photos (not system settings) and do a factory reset (under settings), but you will have to set everything up again. Take care – if you restore from a full backup, it may be infected.
If you are a victim of FluBot or another malware, you can report it here.
You can read other eSafety warnings here.