When security holes are found on devices, you bet we sit up and take notice, and the one discovered this week seems to be a doozy, especially if you have an Android device from Samsung.
Currently working on quite a few Android smartphones – including Samsung’s Galaxy S3 4G – the exploit activates a special code that can send your device spiralling back to what it was like when it shipped in its box, without your phone numbers, music, video, bookmarks, email, and anything that is actually yours.
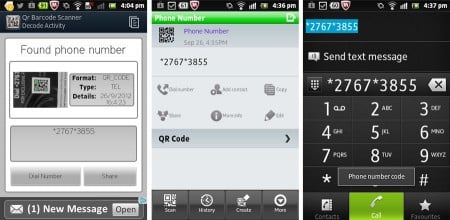
The flaw can be embedded on a webpage quite easily, and when you access the page on a phone – whether through casually browsing to it, typing in the code directly, or more likely hitting a fake advertisement or scanning in a QR code – activates and tells your phone dialer to run it, destroying your life in one fell swoop.
We’ve tested the flaw on several devices, and found that while the dialling function activates on pretty much every Android phone, the factory reset seems to only occur on some, most notably Samsung devices.
For instance, our 3G Samsung Galaxy S3 running Android 4.0.4 won’t even activate the exploit, but the 4G Galaxy S3 we’re reviewing will. Likewise, Samsung’s Galaxy Tab from 2010 will run the flaw, telling us that this will also probably run on Samsung’s range of legacy Android devices, such as the original Galaxy S and cheaper Galaxy 5 (though we don’t have either of those devices to test).
What’s concerning about the older phones is that Samsung doesn’t have active support mediums for them, suggesting that if a patch is released for the newer devices fixing the flaw, it may not be released for the old phones.
How you avoid it
Gizmodo has reported that images advertising the flaw have already started popping up on the web, suggesting that this special code will “unlock the potential” of your Galaxy phone and offer free content.
It won’t, however, and the moment that last hash has been punched in, your phone will start its factory reset and delete everything. It’s a form of social engineering, and will make your day worse.
The best solution here is to not punch that number in. Just don’t do it.
If we can’t be any clearer:
DO NOT TYPE *2767*3855# IN YOUR ANDROID DIAL SCREEN. IT WILL DELETE EVERYTHING.
Even if you don’t have a Samsung Galaxy, don’t risk it. That code is called a USSD, or Unstructured Supplementary Service Data code, and activates functions normally used by phone repair-people.
Some of the codes will work on other handsets, and while we haven’t been able to make it work on a Huawei, Sony, and HTC device, there’s always the possibility yours could be the magic one that makes it happen.

Also be weary of scanning in QR codes on strange images. We’re not sure how many people scan these things in, but many of the QR code programs out there will activate the link automatically, and can contain the code to kill your phone.
As always, you need to be aware of what you’re clicking on and what you’re viewing, so be careful checking emails on your phone from people you don’t know, and make sure not to fall for any advertisements that entice you with ways of making your phone better, more powerful, or unlocking its potential, so to speak.
How you fix it
If Samsung and any other affected manufacturers aren’t releasing patches quick enough for your device – as could definitely happen with legacy devices – then it might be time to install a program called TelStop, which can be found for free on Google’s Play Store.
This acts as a sort of link checker for these exploits. If you accidentally visit one of the links, your phone will prompt you where you want to run that link: your phone or TelStop. If you select TelStop, this will tell you that the link is “likely malicious.”
To test this in action, install the app and head to this page on your phone, a little site run by New Zealand’s Dylan Reeves (who actually details the exploit further) that tells you if you’re likely to have problems.
If the exploit works, your phone will tell you its IMEI code. If not, nothing will happen and you’ll probably just be directed to the dial screen of your phone: phew, you’re mostly safe. Web browsers on computers will ask you how you should run this, and you can just click cancel, as it’s not for you.
This page isn’t dangerous, mind you, because even if it runs without TelStop on your device, all it will do is tell you your phone’s International Mobile Equipment Identity, or IMEI, what is essentially a long serial number specific to your device.
If TelStop is installed, however, you can select it when this code runs and see if the link is dangerous.
It’s probably worth noting that now the exploit is out there, it’s not going to disappear, and this form of security problem will only multiply, so please, be cautious when clicking on links and scanning QR codes.




